How to prevent your email from getting hacked

If you have a computer or a phone, chances are you have at least one email account. Emailing has cemented itself as a vital form of communication and is here to stay. While there are a great many benefits of using email as your form of communication, there has been an epidemic of spam that has polluted our inboxes and will continue to do so.
While most spam emails are relatively harmless, asking you to purchase various pharmaceuticals that are on a limited-time sale (if you are an individual) or to purchase their web design or IT support services (if you are a business), there are a number of emails that can really harm your computer if you engage with that email. Most of us believe we would never fall for something like opening a malicious email because we are too clever and would spot the danger before we make the irreversible click, however, even the best of us may fall victim to these cybercrimes as the criminals improve their tactics and strategies.
The range of these malicious emails stretches far and wide, from the obviously dangerous emails sent by Middle Eastern princes who would like you to hold a few million dollars for them to avoid paying taxes, to an email from your bank or boss that includes important documentation which you must review in a Word document. A recent Data Breach Investigations Report shows that 94% of malware was delivered by email.
Some emails contain graphics and links that are so well replicated, that you have a hard time differentiating it from the real thing. The most dangerous part of it all is that the threat is not always just clicking a link within the email. According to Symantec, the top malicious email attachment types are .doc and .dot which make up 37%, with the next highest being .exe at 19.5%, which means you have to be very careful about opening attachments as well, even if they are in Word document format.
Top Tips To Help You Prevent Your Email From Getting Hacked
With years of experience in IT support, we have seen a lot and done a lot. One of the reasons behind our success with some of our largest clients in Southern Ontario is the trust they have in our capability of maintaining up-to-date knowledge of the cyber threats that exist and may damage their business. While we recommend that any business large or small books a consultation with us about IT support or security awareness training important to protect you and your business, we wanted to share some of our knowledge in this blog to help stop the spread of the cyber pandemic that has polluted so many inboxes worldwide.
1. Use Strong Passwords & 2FA
This topic is a whole blog post of its own, as a matter of fact, we have one that you can read about the use of strong and unique passwords. It also covers 2FA (Two-Factor Authentication) which can be used to protect your email accounts from being accessed by those you don’t want.
To sum up this point in one go, you should always have unique passwords that use all the elements of strong passwords described in the blog post above, and preferably you should rotate them once in a while using a password manager.
2. Watch Out For Suspicious Emails
You have read the blog post linked above and your email is the digital version of Fort Knox. Congratulations on taking the first step! You would be surprised how many emails get hacked because these simple steps that can be followed are simply ignored.
Unfortunately, that was just the first step. Now that you are the only one who has access to your sacred inbox, you have to make sure that you treat it with the necessary care and you are vigilant about what you do with your emails.
There are many reasons why your email might fall into the hands of a hacker or a cyber-criminal. Sometimes there are large data breaches that expose millions of accounts (or even billions in the recent case with Yahoo where 3 billion accounts were hacked). Sometimes, however, you simply cannot escape this threat as hackers create a randomized attack and you just happen to “win the lottery”, the same way billions of other people do.
Fortunately, opening the email itself doesn’t mean that you have been hacked. Of course, we recommend reading the email address it was sent from and the subject line before opening that email, but if that train has left the station don’t panic – there is a way out. Look at the email address very carefully because often the hacker disguises the name of the company in a subdomain to make it look legitimate while the domain they are actually using installs malware on your computer or phone.
Before you click on anything, whether it is an attachment or a link be very careful about analyzing the email and differentiating between real and fake. If the logos or pictures are of poor quality or look outdated, or if the email text looks disarranged, this can be a red flag that it’s a malicious email. Any attachment can install malware on your computer, and just because a link says something doesn’t mean it doesn’t go to a completely different URL.
One good trick you can also use if you are not sure about the email legitimacy is not opening it on your phone. Opening emails on a phone is the easiest way to open a malicious email because you cannot hover over the links and check them. On a desktop, you can actually hover over a link and confirm the URL and where it is heading (being careful to not actually pull that mouse trigger and click it by accident), which may reveal the hidden destination the hacker intends for you to visit.
This system is not foolproof, however, because it still doesn’t prevent you from opening a malicious attachment which can disguise itself as a friendly file. If at this point you are still not sure about the legitimacy of this email or are simply too afraid about your mouse trigger-finger, we recommend contacting the company or person sending you that email and making sure that they actually sent you that email.
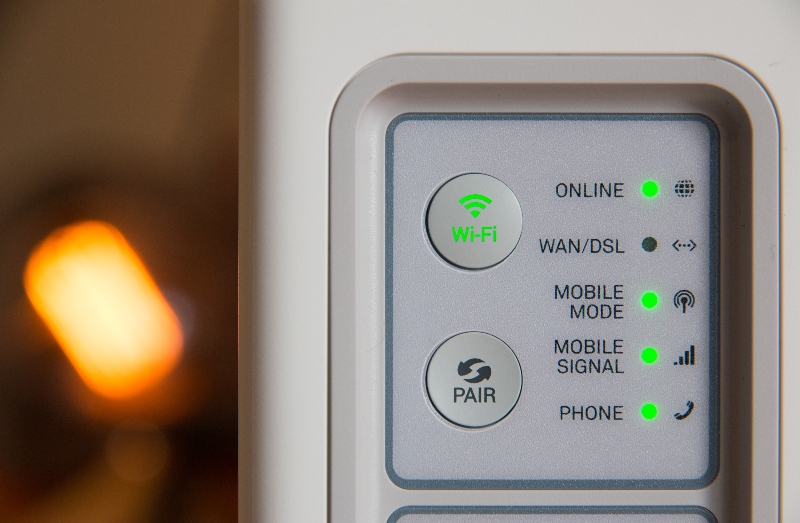
3. Using Secure Wi-Fi
First and foremost we recommend not using public Wi-Fi if you want to ensure the utmost security. I know this can rack up your data bill, but this has become an increasing source of cyber attacks all over the world. If you would like to learn more about the dangers of this we recommend reading our blog post about protecting your smartphone from hackers.
Once you avoid hooking up to public Wi-Fi you’re halfway there. The next element of this is to ensure that your home (or office) router and Wi-Fi are secured. When you’re initially setting up your home network you will be asked to create a publicly visible network name, otherwise known as an SSID (Service Set identifier). Most devices are configured with a default network name that has been assigned by the manufacturer of that device. Changing the default name to make it more difficult for a hacker to know what type of router you have is imperative to reduce the chance of attack.
Need help with your office network? That’s one of our favorite things to do at Dunham Connect! Over the years we have helped hundreds of clients of all sizes safely secure office networks at lightning speeds.
Take Action!
Are you or your company getting bombarded by spam and malicious emails? While we hope you found this article useful and that it helps you prevent future attacks, we can do a lot more than just help with the power of our words. Our team of IT experts can help you implement everything from end-to-end encryption to installing spam filters on your website or even providing security awareness training for your company to help protect you and your employees.
Learn more about our email protection and IT services.
Leave a Comment